Leaked: Britain Exports GCHQ's Dark Arts Overseas
All my investigations are free to read, thanks to the enormous generosity of my readers. Independent journalism nonetheless requires investment, so if you value this article or any others, please consider sharing, or even becoming a paid subscriber. Your support is always gratefully received, and will never be forgotten. To buy me a coffee or two, please click this link.
Leaked documents expose how prolific Western government contractor Torchlight, staffed by British military and intelligence veterans, has covertly trained “commercial and government clients” the world over in GCHQ’s digital espionage and cyberwar strategies. Cloak-and-dagger techniques to “discredit, disrupt, delay, deny, degrade, and deter” target adversaries and populations, honed for kinetic and psychological warfare and regime change overseas, have become a commodity, open for unregulated use by undisclosed private sector and state actors.
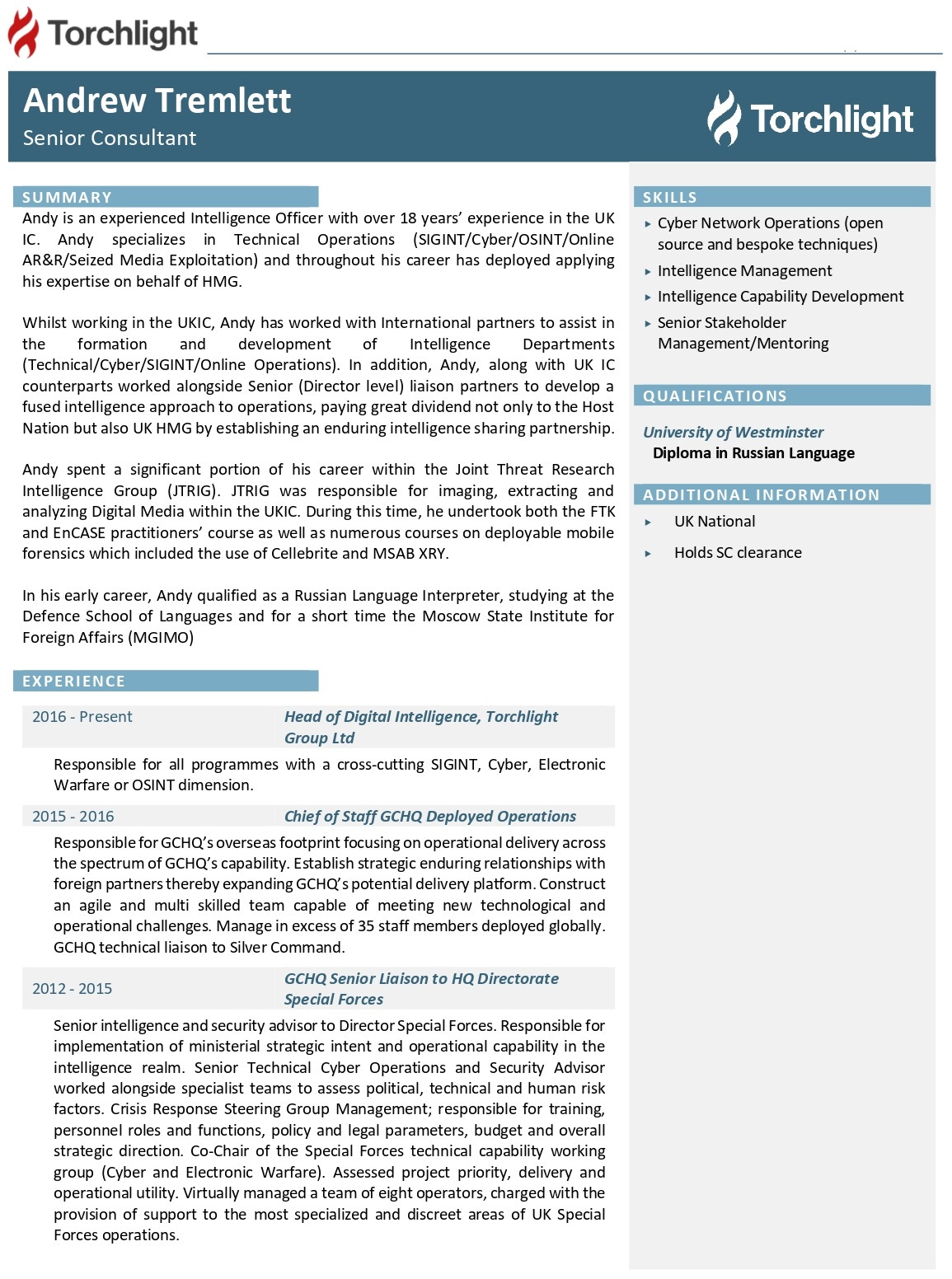
Central to these efforts was GCHQ journeyman Andrew Tremlett. While serving as Torchlight’s head of digital intelligence, he was “responsible for all programmes with a cross-cutting SIGINT [signals intelligence], cyber, electronic warfare or OSINT [open source intelligence] dimension.” A leaked CV notes he spent over 18 years toiling for British intelligence, “primarily” GCHQ. One of his key duties was “[working] with international partners to assist in the formation and development of intelligence departments.” In other words, constructing analogues of MI5, MI6 and GCHQ abroad.
This activity reportedly paid a “great dividend not only” to the “host nation” in question, but also the British government, “by establishing an enduring intelligence sharing partnership” between the pair. However, Tremlett “spent a significant portion of his career” within GCHQ’s notorious Joint Threat Research Intelligence Group (JTRIG). Exposed by NSA leaker Edward Snowden in 2014, this shadowy unit plays a “major part” in GCHQ’s activities, executing the agency’s most depraved operations.
This includes cyberattacks and propaganda efforts, such as pushing “mass messaging” against target countries, organizations, groups and individuals via social media platforms, with an emphasis on “unsavory information”. “False flag” connivances, in which JTRIG conducts malign actions designed to appear as if an adversary was responsible, is likewise a core component of the unit’s remit. JTRIG was heavily involved in spreading pro-insurrectionary messaging during the Arab Spring, while attempting to overthrow Zimbabwe’s longtime ruler Robert Mugabe, and prevent Argentina taking over the Falklands.
On top of establishing “strategic enduring relationships with foreign partners thereby expanding GCHQ’s potential delivery platform,” Tremlett provided “direct specialist intelligence support” to British special forces, including the SAS, in “counter-terrorism” and “counter insurgency”. This placed him in charge of supporting “the most specialized and discreet areas of UK special forces operations.” Tremlett’s experience in these fields was duly harnessed by Torchlight as a major selling point, when pitching its training programs to “commercial and government clients.”
‘Device Seizure’
Other leaked Torchlight documents offer candid insight into the firm’s training of “government clients”, clandestinely delivered on London’s dime. For example, from June 2019 - March 2020, the firm sought to enhance “the ability of evidence gathering agencies” by Jordan’s most secretive security and intelligence services, specifically in the field of “digital media exploitation”. Alumni learned “to effectively extract data from digital devices,” assisting domestic surveillance and prosecutions, while “[enabling] the sharing of evidence” between Amman and London.
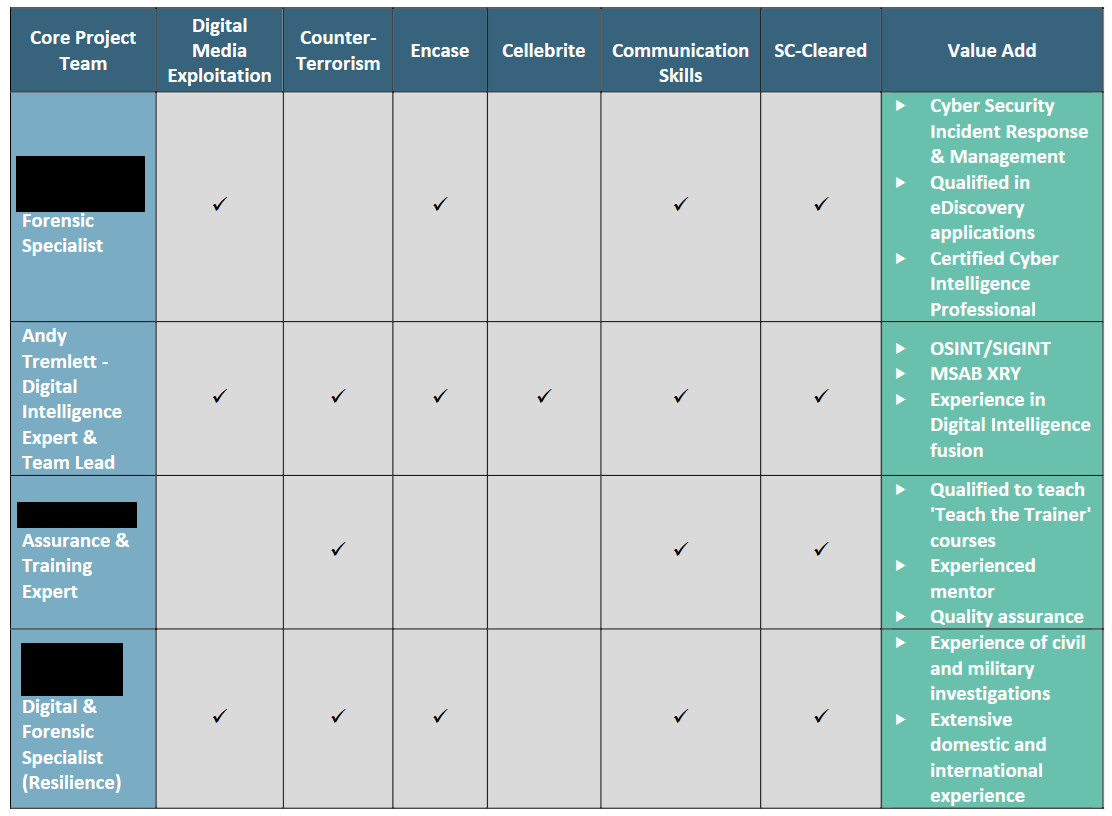
Andrew Tremlett led the initiative. Project files note he was “instrumental in determining” Jordan’s “requirement” in the desired fields. After visiting the headquarters of Amman’s Public Security Directorate, the GCHQ journeyman “was able, through close collaboration, to review digital forensics documentation, conduct a physical site survey, observe digital forensic practices, and undertake an informal discussion with members of staff to gauge levels of skills [and] training, understanding and awareness.” This insider knowledge, it was forecast, would be “pivotal in delivering real change and capability improvement.”
Tremlett’s key takeout was Jordan’s digital forensics specialists were “satisfactorily equipped” in respect of hardware and software, “but were not adequately trained to fully exploit the potential of the equipment they possess.” They were also unable to utilise these resources “to enable UK – Jordan cooperation or evidence sharing.” For example, Amman’s spooks use EnCASE, a court-approved digital forensics suite that can analyze, collect and preserve evidence gleaned from digital devices. Likewise, Jordan’s spying apparatus employs FTK, capable of uncovering hidden or deleted data, including browsing history, from hard drives and smartphones.
Most disquietingly, Amman’s intelligence apparatus also enjoy access to Cellebrite. Controversies surrounding the Israeli-created “forensics” tool have abounded ever since its 2007 launch. The firm has dispatched representatives to Saudi Arabia to hack into smartphones. Cellebrite’s tech frequently supports prosecutions of dissidents in Bahrain, presaging their detentions, torture, and extended imprisonment on political charges. Between 2017/18, Cellebrite assisted the Western-backed government of Myanmar’s persecution of Reuters reporters, who revealed state-directed genocidal attacks on the country’s Rohingya population.
Such scandals have been no deterrent to Western governments widely adopting the company’s technology. It is evident British police, security and intelligence agencies are no exception. The leaks record how Tremlett is an expert in Cellebrite’s use. His “significant” experience in the field would purportedly provide Jordan “additional perspective of digital exploitation and how intelligence gained from device seizure and analysis can enhance and drive the intelligence cycle and enrich other intelligence sources,” such as “open source” spying.
That Amman was covertly taught GCHQ’s darkest arts is disturbing. It is an imprisonable offence to criticize the country’s ruler, King Abdullah II – a member of the Hashemite dynasty installed by the British following World War I, and British Army veteran – or state officials and institutions. Countless individuals rot in jail for mild condemnation of Amman’s ruling elite online. Journalists at home and abroad perpetually walk on eggshells, liable for arrest and imprisonment if they publish “fake news” about Jordan’s government.
Repression in Jordan ratcheted significantly in the wake of the Gaza genocide’s eruption. By April 2024, at least 1,500 people had been arrested for participating in Palestine solidarity protests. Many activists were targeted under Amman’s widely-criticized Cybercrime Law, which criminalizes political speech on social media. In 2021 alone, the year after Torchlight’s training ended, there were 6,605 separate prosecutions under the sweeping legislation. More recent figures are unavailable.
‘Online Behaviour’
In this context, it is noteworthy Tremlett’s GCHQ position focused heavily on “counter-terrorism” and “counter insurgency”. Leaked slides of a 2012 JTRIG presentation offer some examples of how the unit targeted overseas opponents in this manner. Indeterminate “Iran work” was opaquely cited as a successful example of “blog writing” efforts. “Significantly disrupting” the Taliban by bombarding the group with a “blizzard” of text messages, calls, and faxes, while deleting its members’ “online presence”, was likewise venerated. The latter approach was praised as “very annoying!!”.
Tremlett’s expertise in “seized media exploitation” as a result of his JTRIG service also raises questions about what “commercial and government clients” are truly being taught by Torchlight. The leaked JTRIG presentation makes repeated reference to planting information on “compromised” target devices, including “potential ‘damming’ [sic] information, where appropriate.” Cellebrite of course allows end users to break open captured smartphones and computers. The ease with which falsely incriminating data could be placed in seized devices is evident.
Elsewhere, the presentation sets out methods to “discredit a target”. First and foremost: “set up a honey trap…a great option…very successful when it works…get someone to go somewhere on the internet, or a physical location to be met by a ‘friendly face’. JTRIG has the ability to ‘shape’ the environment on occasions.” Other options included changing a target’s “photos on social networking sites,” writing a blog post “purporting to be one of their victims,” and emailing or texting “their colleagues, neighbours, friends etc.”
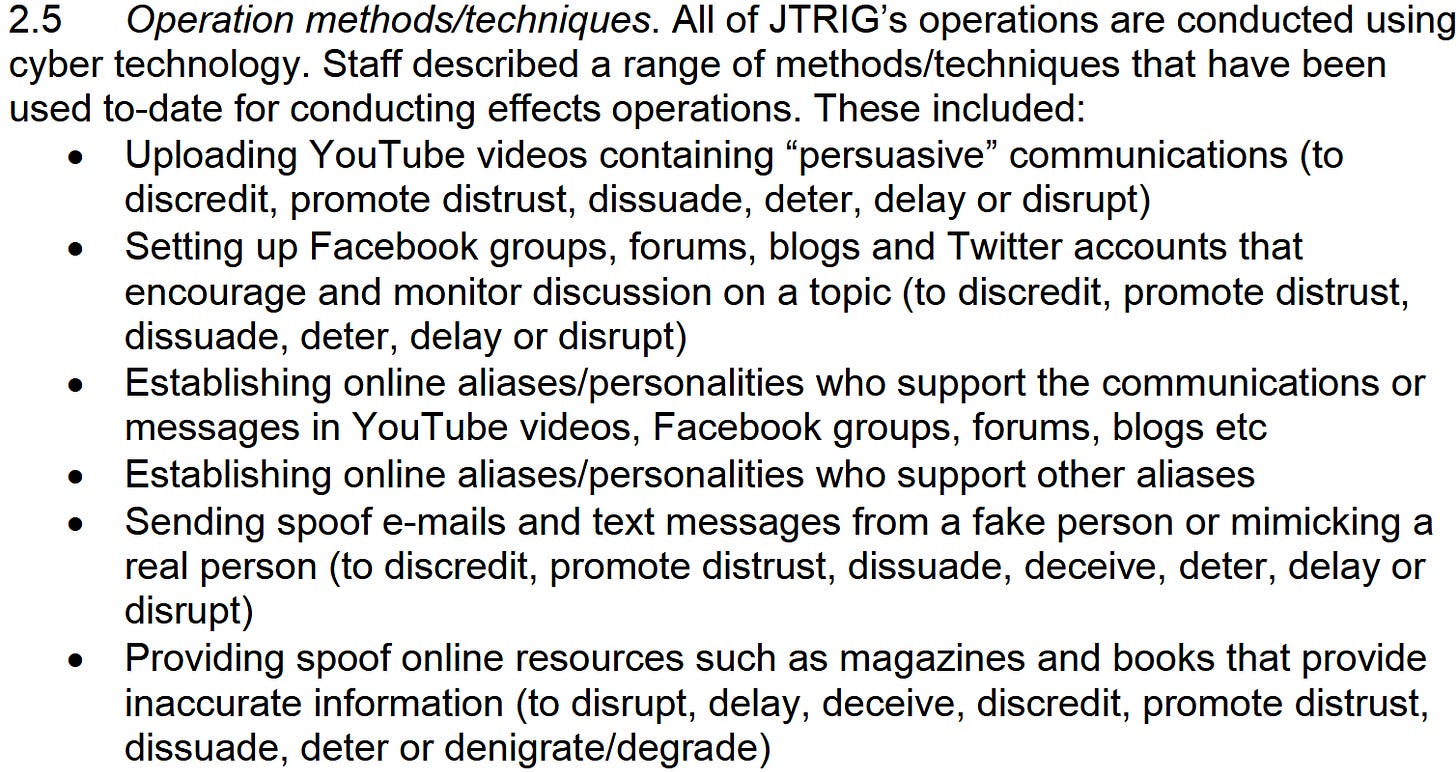
A separate leaked document on JTRIG’s operations notes the unit is engaged in “uploading YouTube videos containing ‘persuasive’ communications…setting up Facebook groups, forums, blogs and Twitter accounts that encourage and monitor discussion on a topic…Establishing online aliases/personalities who support the communications or messages in YouTube videos, Facebook groups, forums, blogs etc…Establishing online aliases/personalities who support other aliases.” JTRIG also sets up “spoof trade sites…that may take a customer’s money and/or send customers degraded or spoof products.”
The document furthermore provides examples of JTRIG’s online human intelligence endeavors. Such initiatives “typically involve establishing an online alias/personality who has a Facebook page, and membership of relevant web forums.” These false personae then “befriend” a target in order to spy on them, or influence their behavior. “Interactions with the target may be informed” by a combination of signals intelligence, “monitoring of the target’s online behaviour,” and intelligence gathered by MI6 “on-the-ground.” Online interactions can in turn “facilitate [MI6] contact” in real life.
In detailing JTRIG’s “counter-terror” initiatives targeting Muslims at home and abroad, and Irish republicans, the unit was reportedly involved in “disrupting the dissemination of extremist material over the internet; discrediting extremist sites and individuals/groups; conducting online [human intelligence]; and hosting extremist sites” in order to entrap individuals in an astroturf dragnet. Tremlett’s role in tutoring Torchlight’s corporate and governmental clients in tricks of the “electronic warfare” trade suggests these strategies are now far from JTRIG’s unique preserve.
In the process, untold parties now possess the technology and insight to replicate JTRIG’s chaos-wreaking specialities on their own rivals, adversaries and populations, without oversight or public cognisance. It is all but inevitable countries such as Jordan, if not many others, have employed the unit’s techniques to ensnare Palestine solidarity activists, and other troublesome ‘enemies within’. Little will victims know the trail of their repression leads straight back to London, courtesy of Torchlight.



I feel that we'll be seeing British dark arts deployed in Budapest this next week.
What? - Against the wishes of their US overlords? This is where interests clearly diverge, despite all the kowtowing to Trump's regime on the part of the Starmer vassal state.
Great article! The global reach of these agencies is mind blowing.